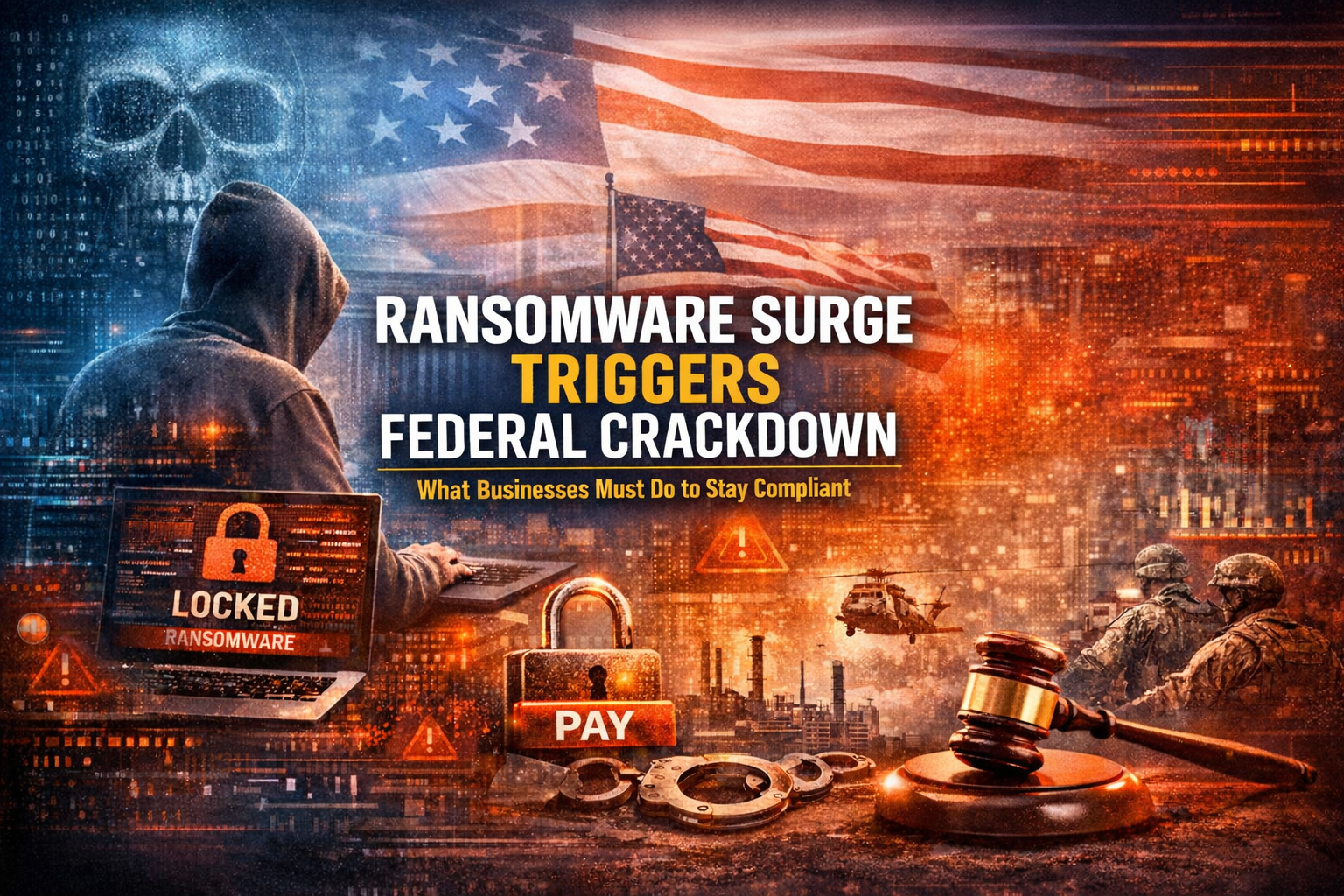
Cybersecurity is no longer just an IT issue—it’s a national security and regulatory priority.
Ransomware attacks are rising at an alarming pace, and federal agencies like Cybersecurity and Infrastructure Security Agency (CISA), Department of Justice (DOJ), and Federal Bureau of Investigation are responding with stronger guidance, increased enforcement, and coordinated action across industries.
The message is clear: Organizations are now expected to prevent, detect, and report ransomware—not just recover from it.