The $6.8 Billion Wake-Up Call: Why 2025 Changed Federal Cybersecurity Enforcement Forever
For years, cybersecurity was often treated as a "check-the-box" IT requirement for government contractors. Those days are officially over.
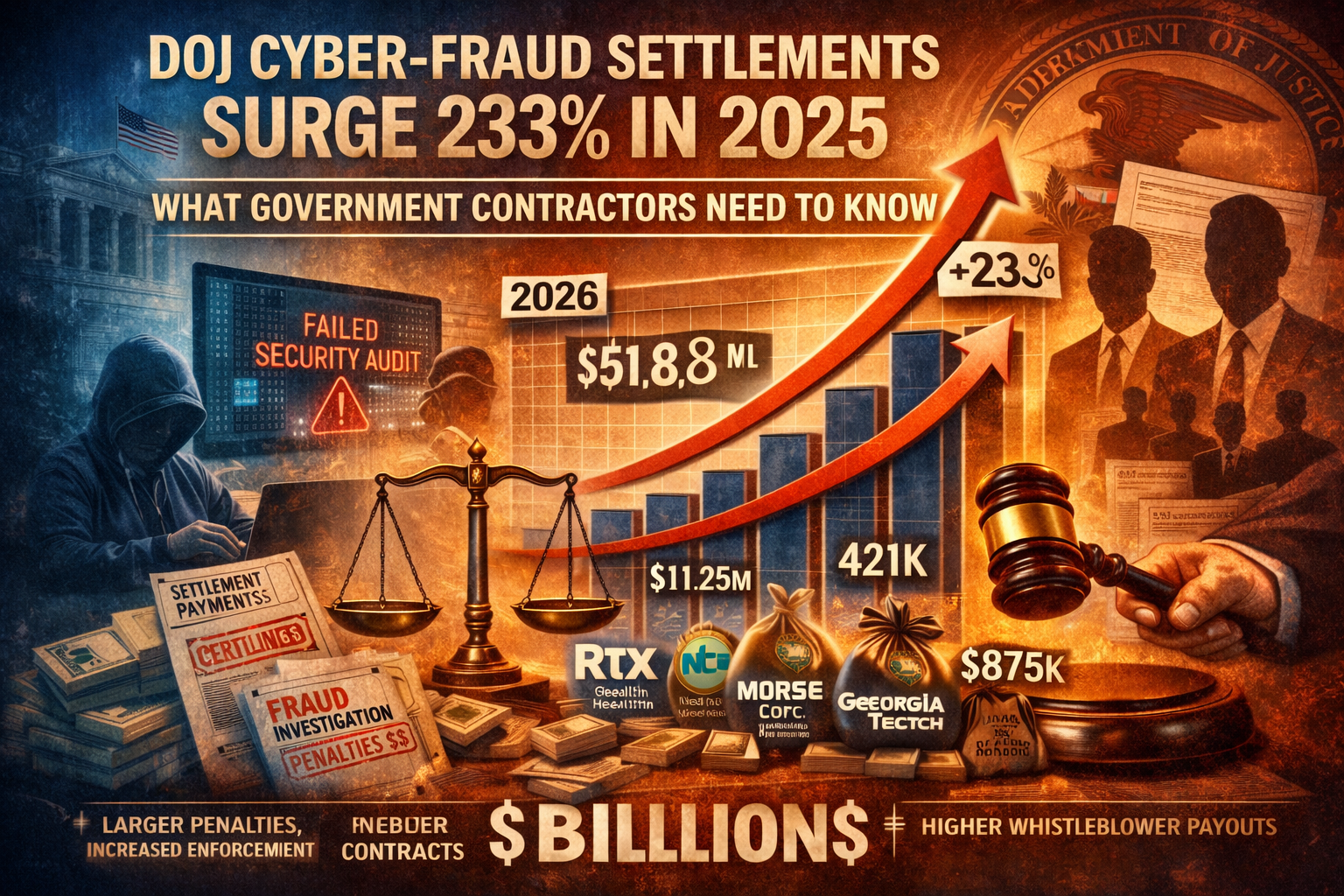
The Department of Justice (DOJ) just dropped its 2025 numbers, and the data tells a chilling story: Civil Cyber-Fraud settlements have skyrocketed by 233% in just twelve months. With total False Claims Act (FCA) recoveries surpassing $6.8 billion last year—the highest in history—the DOJ isn't just watching; they are actively hunting.
The Numbers Behind the Surge
In 2024, cybersecurity settlements totaled roughly $15.5 million. In 2025, that number exploded to nearly $52 million. This isn't a statistical fluke; it’s the result of the DOJ’s Civil Cyber-Fraud Initiative hitting its full stride in its fifth year.
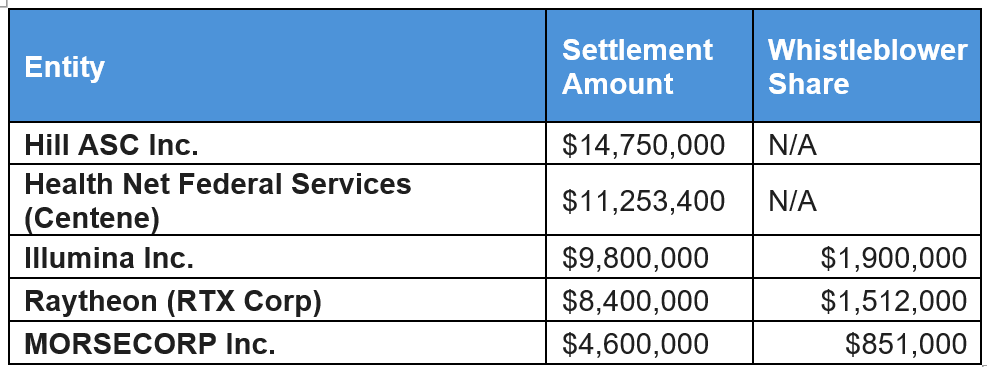
2025 Settlement Breakdown
The DOJ is casting a wide net, catching everything from defense giants to specialized research labs.
5 Hard Truths for Contractors in 2026
1. No Company is "Too Small" to Target
Think the DOJ only cares about the Tier 1 defense firms? Think again. While names like Raytheon and Georgia Tech made headlines, smaller firms like Swiss Automation ($421k settlement) were also caught in the dragnet. If you have a federal contract, you have a target on your back.
2. Industry Agnostic Enforcement
Cybersecurity is no longer just a "Defense" problem. In 2025, the DOJ pursued contractors in genomic sequencing, healthcare, and telecommunications. If your contract involves federal data or systems, the cybersecurity standards are non-negotiable.
3. The "Whistleblower" Economy is Booming
The role of the qui tam relator (whistleblower) is more prominent than ever. In 2025, whistleblowers took home over $4.5 million in rewards from these cases. Your most significant compliance risk might be a disgruntled employee or a savvy competitor who notices your protocols don't match your promises.
4. Deficient Products = Fraud
The DOJ is focusing on three specific "sins":
Selling cybersecurity products that don't actually meet federal specs.
Lying about your internal security protocols to win a bid.
Failing to report a breach when you are legally obligated to do so.
5. Treble Damages are the "New Normal"
Under the False Claims Act, the government can seek triple damages. A $5 million mistake can quickly become a $15 million corporate catastrophe that threatens the very existence of your business.
How to Protect Your Firm
The shift from "IT issue" to "Legal & Compliance issue" is complete. To survive this era of aggressive enforcement, contractors must:
Audit Your Representations: Ensure that what your BD team promises in a proposal matches what your IT team is actually doing.
Document Everything: In an FCA investigation, if it isn't documented, it didn't happen.
The Self-Reporting Dilemma: If you discover a flaw, self-reporting (with the guidance of counsel) can significantly reduce penalties. However, doing this incorrectly can be just as risky as staying silent.
The Bottom Line: Cybersecurity compliance is no longer a "nice to have"—it is a core requirement of doing business with the U.S. Government. The 233% surge in settlements proves that the DOJ is no longer giving out warnings; they are giving out bills.
Is your compliance program ready for a DOJ audit? Don't wait for a whistleblower to tell you the answer.
Ready to see where your company defenses stand?
👉 Request your customized cyber vulnerability report today and stay ahead of threats.
👉 Gain insights into your unique cybersecurity vulnerabilities with a custom report.
👉 Train your team to be your first line of defense
📞 Schedule a call today or 📧 contact us for a consultation.