CMMC 2.0: The Path to Compliance and the Critical Role of Executive Affirmations
The Department of Defense (DoD) has officially entered a new era of cybersecurity. With the finalization of the Cybersecurity Maturity Model Certification (CMMC) program, the "honor system" for defense contractors is effectively over. For the 220,000+ companies in the Defense Industrial Base (DIB), the focus has shifted from planning for CMMC to executing it.
As we move through the phased implementation that began on November 10, 2025, contractors must understand not just the technical controls, but the legal accountability that now sits at the heart of the program: the Annual Affirmation.
Part 1: CMMC 2.0 – The Three-Tiered Framework
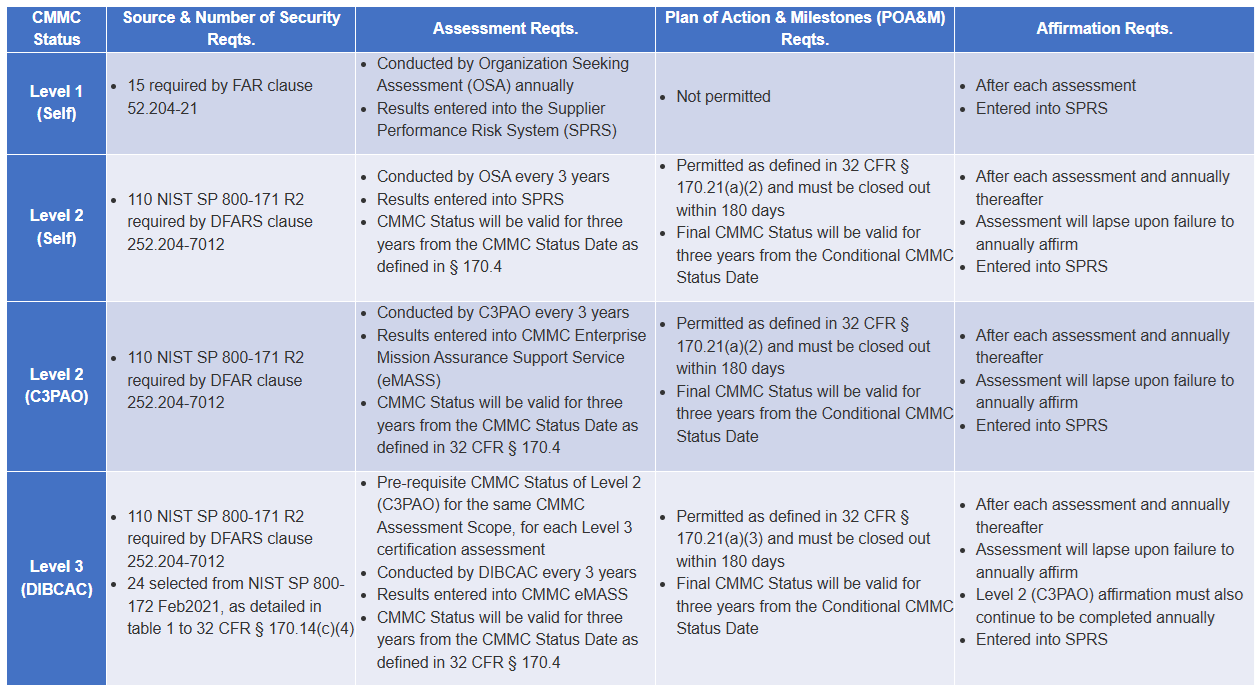
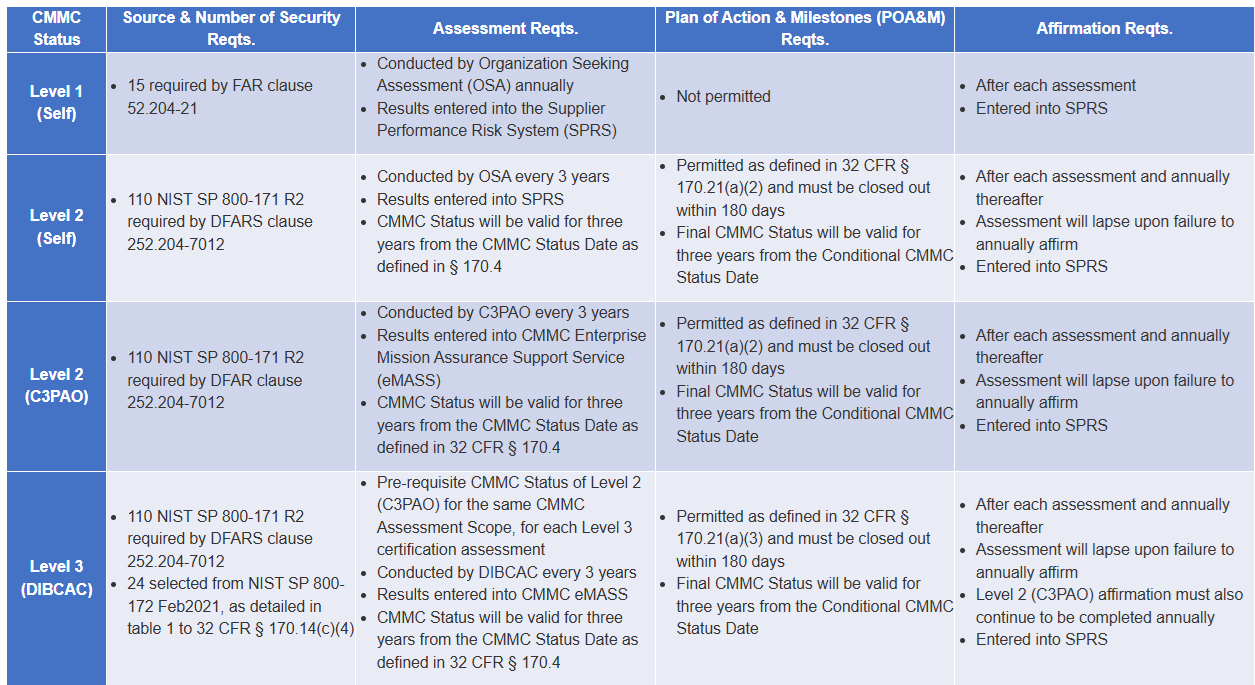
To ensure national security, the DoD requires contractors to protect sensitive information at a level commensurate with the risk. CMMC 2.0 simplifies this into three distinct levels:
Level 1 (Foundational): Focused on protecting Federal Contract Information (FCI). It consists of 15 basic security requirements (derived from FAR 52.204-21). Compliance is verified through an annual self-assessment.
Level 2 (Advanced): Focused on protecting Controlled Unclassified Information (CUI). This level aligns exactly with the 110 controls of NIST SP 800-171. Depending on the contract, compliance requires either a self-assessment or a triennial assessment by a Certified Third-Party Assessment Organization (C3PAO).
Level 3 (Expert): Reserved for high-priority programs handling the most sensitive CUI. It adds requirements from NIST SP 800-172 and requires triennial assessments led by the DoD’s own DIBCAC team.
Part 2: The Deep Dive – Understanding the Annual Affirmation
Source: Department of Defense
The most significant change in CMMC 2.0 isn't just what you secure, but who signs off on it. Under 32 CFR § 170.22, the DoD now requires a formal affirmation of compliance. This is no longer just a technical task for the IT department—it is a legal mandate for company leadership.
1. Who is the "Affirming Official"?
The affirmation must be submitted by a senior level representative from your organization. This is typically the CEO, CFO, or a senior executive who has the authority to ensure the organization remains in compliance. This official is personally responsible for attesting that the security requirements have been implemented and will be maintained.
2. When Must You Affirm?
Affirmations are not a one-time event. They must be submitted electronically via the Supplier Performance Risk System (SPRS) in the following instances:
Initial Achievement: Upon achieving a "Conditional" or "Final" CMMC status.
Annually: Every year following the "Final CMMC Status Date" to confirm continuing compliance.
POA&M Closeout: Following the completion of any Plan of Action and Milestones (POA&M) to confirm that gaps have been officially closed.
3. Why the Affirmation Matters: Legal Accountability
The affirmation serves as a formal statement that your company is meeting its contractual obligations. By signing, the official is attesting "under penalty of law" that the controls are in place.
False Claims Act (FCA) Risk: If an organization submits an affirmation while knowing they are not in compliance, they risk litigation under the Department of Justice’s Civil Cyber-Fraud Initiative.
Contract Eligibility: Under DFARS 252.204-7021, having a current, valid affirmation in SPRS is a condition of contract award. If your annual affirmation lapses, you may be ineligible to bid on new work or have options exercised on current contracts.
Part 3: The Implementation Timeline – Where Are We Now?
The DoD is rolling out CMMC in four phases to allow the industry time to adjust:
Phase 1 (Now Underway): CMMC requirements for Level 1 and Level 2 self-assessments are appearing in new solicitations.
Phase 2 (Starting Nov 2026): Level 2 C3PAO (third-party) certification becomes a mandatory condition of award for a broader range of contracts.
Phase 3 (Starting Nov 2027): Level 2 certification becomes universal, and Level 3 requirements begin to appear in solicitations.
Phase 4 (Starting Nov 2028): Full implementation across all applicable DoD solicitations and contracts, including option periods.
Strategic Next Steps
For contractors, the message is clear: Cybersecurity is now a core business function.
1. Identify Your Data: Determine if you handle FCI or CUI to identify your target CMMC Level.
2. Verify Your Controls: Perform a gap analysis against NIST SP 800-171.
3. Prepare Your Leadership: Brief your senior executives on the affirmation requirements now. Ensure they understand the evidence behind the security claims they will be required to sign.
By treating CMMC as a strategic priority rather than a compliance hurdle, your organization can protect national security while securing its own future in the defense industrial base.
For official guides and technical documentation, visit the DoD CIO CMMC Resources page.
👉 Request your customized cyber vulnerability report today and stay ahead of threats.
👉 Gain insights into your unique cybersecurity vulnerabilities with a custom report.
👉 Train your team to be your first line of defense
📞 Schedule a call today or 📧 contact us for a consultation.